The Complete Ethical Hacking Course Beginner to Advanced
Discover how to do honest hacking, penetration testing, internet screening, and even wifi hacking using kali linux!
Gain the capacity to do ethical hacking and also penetration screening by taking this program! Get the answer from an experienced IT expert to each concern you have associated with the discovering you perform in this course consisting of mounting Kali Linux, utilizing VirtualBox, basics of Linux, Tor, Proxychains, VPN, Macchanger, Nmap, splitting wifi, aircrack, DoS strikes, SLL strip, recognized susceptabilities, SQL injections, fracturing Linux passwords, and a lot more subjects that are included every month!
If you resemble me, you are reading so much more currently because you want to know for certain whether this course is worth taking prior to you spend your cash as well as time in it. More than10,000 people have actually currently completed the process of determining to take this training course and even I really hope discussing a few of their experiences can verify useful for you here. Below are what 3 current pupils needed to claim in the reviews in their own words.
If you intend to learn more about exactly what the course consists of, right here is a short list of questions to assist you choose if you ought to take it adhered by a deep list of the program lectures here. Exactly what you see is simply the beginning of just what the training course includes due to the fact that Ermin is making brand-new talks each month for you! You will reach see display capture live tutorials revealing you everything you need to do to obtain started with honest hacking as well as seepage screening consisting of information about all of the subjects listed below!
Introduction to The Complete Ethical Hacking Course Beginner to Advanced (AIOVideo.com)
Ways to mount VirtualBox.
Exactly what to do to create the virtual setting.
Mounting VirtualBox in a Windows 8.1 setting.
Basic Linux terminal.
Remaining confidential with tor.
Digital Private Networks (VPN).
You obtain lifetime access to this course which currently has 20+ hours of HD video tutorials discussing every little thing you have to be a seepage screening expert and even moral hacker! If you are still certain, below are 3 concerns you could make use of making the decision!
Do you wish to find out how you can penetrate networks, exploit systems, burglarize computer systems, and compromise routers?
Do you intend to utilize the valuable abilities to help companies that desire you to make use of these abilities to test their network security and even show them to enhance it?
Just how would certainly you feel if you could apply these abilities to just what you already understand to significantly progress your profession as a network professional, network administrator, or freelancer online?
If you answered yes to any of these concerns, I would certainly presume based upon my encounter teaching 50,000+ students on Udemy that you may enjoy this course. If for any sort of reason I am wrong, you have 1 Month to ask Udemy for a reimbursement. With 98 % of pupils appreciating this program sufficient to not request for a refund as well as 50+ pupils uploading excellent testimonials, I can think the odds of you enjoying this training course are extremely high!Thank you very much for reviewing all of this! Ermin and I intend to see you as a student in the course when we next fulfill!
What are the requirements?
- Reliable and fast internet connection.
- Wireless networking card.
What am I going to get from this course?
- Over 113 lectures and 25 hours of content!
- Answers to every single question you have about ethical hacking and penetration testing from an experienced IT professional!
- Tips for remaining anonymous in hacking and penetration testing activities.
- A guide to using these skills to get a better job and make money online as a freelancer.
- The ability to secure and protect any network from hackers and loss of data.
- A complete tutorial explaining how to build a virtual hacking environment, attack networks, and break passwords.
- Step by step instructions for insulation VirtualBox and creating your virtual environment on Windows, Mac, and Linux.
What is the target audience?
- You can begin this course with any level of knowledge and quickly start advancing your skills as an information technology and security expert anywhere in the world!
- If you are working to advance your career on LinkedIn or as a freelancer online, you can use the skills you build in this course to get a better job and to increase your hourly pay rate.
- If you are hoping to be a better network administrator, you can use this course to learn how to secure networks and protect assets.
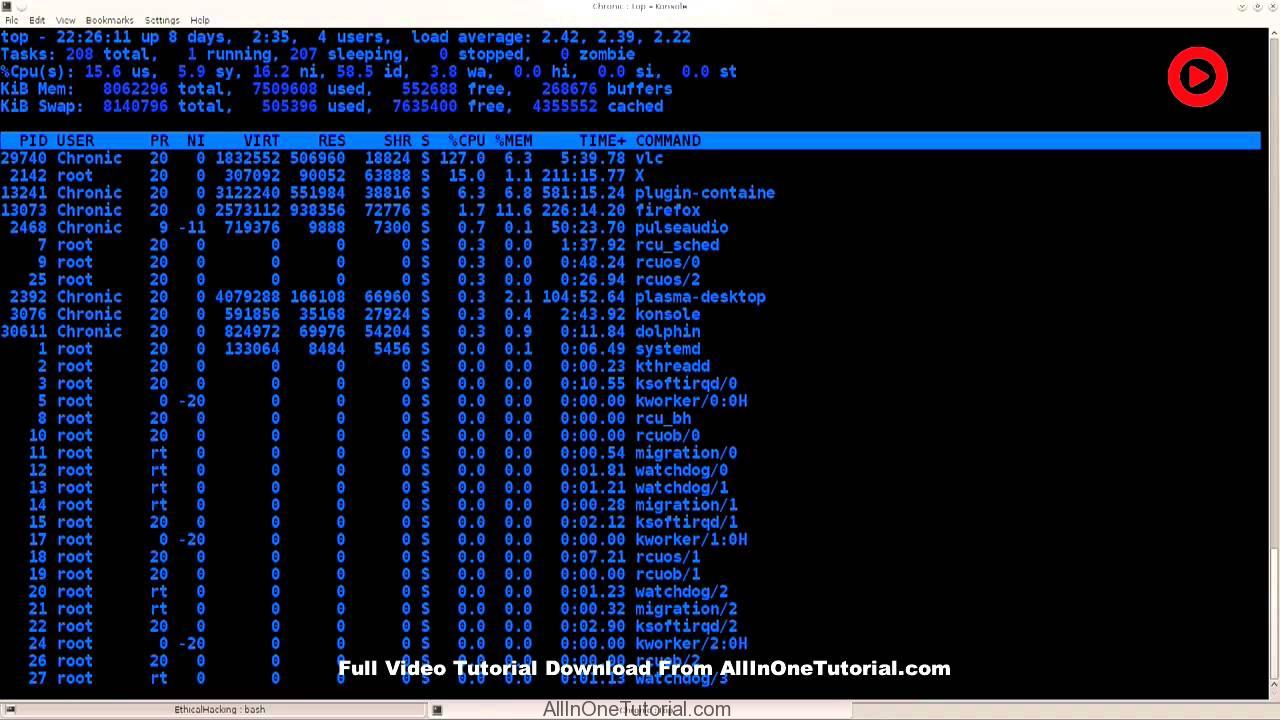
Screenshot:
Courses include:
| Section 1: Ethical hacking and penetration testing. What is it and how can you use it? | |||
|---|---|---|---|
| Lecture 1 |
Thank you for taking this course! What is the most it can do for you?
|
01:35 | |
| Lecture 2 |
How can you earn money legally with your ethical hacking skills online?
|
04:19 | |
| Lecture 3 |
What is hacking? Here is the definition we use in the course.
|
02:30 | |
| Lecture 4 |
What do you hope to gain from learning about hacking?
|
02:33 | |
| Lecture 5 |
How to get answers to your questions and help with problems?
|
03:39 | |
| Lecture 6 |
Unlock your certificate and upgrade your LinkedIn profile using this course!
|
02:58 | |
| Section 2: Prerequisites for getting started with this course. | |||
| Lecture 7 |
Introduction to Ethical Hacking. What is it in detail?
|
08:02 | |
| Lecture 8 |
Prerequisites success tips for getting the most out of this course.
|
07:28 | |
| Lecture 9 |
How can you become intermediate and advanced with this course?
|
03:40 | |
| Section 3: Basic hacking terms you will want to know getting started. | |||
| Lecture 10 |
Basic terminology such as white hat, grey hat, and black hat hacking.
|
12:00 | |
| Lecture 11 |
Basic terminology including SQL injections, VPN , proxy, VPS, and key loggers.
|
18:18 | |
| Section 4: Build your hacking environment! | |||
| Lecture 12 |
Getting started successfully PDF with common questions answered and helpful tips
|
35 pages | |
| Lecture 13 |
Installing VirtualBox with rpm plus why use a virtual machine.
|
08:58 | |
| Lecture 14 |
Installing VirtualBox using the default package manager from repositories.
|
15:01 | |
| Lecture 15 |
Creating the virtual environment.
|
13:35 | |
| Lecture 16 |
Installing VirtualBox in a Windows 8.1 environment.
|
05:16 | |
| Lecture 17 |
Kali Linux installation within a virtual environment.
|
16:00 | |
| Lecture 18 |
Kali Linux installation after it is running and getting starting using it.
|
12:18 | |
| Lecture 19 |
Installing VirtualBox Guest Additions
|
14:40 | |
| Section 5: Set up instructions for Mac users ONLY | |||
| Lecture 20 |
Installing VirtualBox on a Mac
|
18:09 | |
| Lecture 21 |
Setting up Kali Linux with VirtualBox part 1
|
13:38 | |
| Lecture 22 |
Setting up Kali Linux with VirtualBox part 2
|
15:23 | |
| Lecture 23 |
How to set up a USB passthrough on a Mac part 1
|
19:02 | |
| Lecture 24 |
How to set up a USB passthrough on a Mac part 2
|
09:00 | |
| Lecture 25 |
Kali Linux Live USB on a MacBook Pro part 1 ( OPTIONAL )
|
19:47 | |
| Lecture 26 |
Kali Linux Live USB on a MacBook Pro part 2 ( OPTIONAL )
|
11:37 | |
| Lecture 27 |
Kali Linux Live USB on a MacBook Pro part 3 ( OPTIONAL )
|
13:40 | |
| Section 6: How to create a bootable USB of Kali Linux ( optional ) | |||
| Lecture 28 |
How to create a bootable USB of Kali with persistent storage > 4 GB part 1
|
19:17 | |
| Lecture 29 |
How to create a bootable USB of Kali with persistent storage > 4 GB part 2
|
18:01 | |
| Lecture 30 |
How to create a bootable USB of Kali with persistent storage > 4 GB part 3
|
06:26 | |
| Lecture 31 |
How to create a bootable USB of Kali with persistent storage > 4 GB part 4
|
10:48 | |
| Section 7: Updates: How to install VirtualBox on Fedora 22 + Kali Sana VM ( OPTIONAL ) | |||
| Lecture 32 |
Fedroa 22 VirtualBox set up
|
17:10 | |
| Lecture 33 |
Kali Sana virtual machine installation
|
05:37 | |
| Lecture 34 |
How to install VBox GuestAdditions in Kali Sana
|
07:13 | |
| Section 8: Linux Terminal including basic functionalities and CLI. | |||
| Lecture 35 |
Introduction to the Linux terminal.
|
09:31 | |
| Lecture 36 |
Linux Command-Line Interface (CLI) basics.
|
14:04 | |
| Lecture 37 |
The Linux CLI explained in greater detail to give you a good understanding.
|
15:26 | |
| Section 9: What is Tor? How can you use it to protect your anonymity online? | |||
| Lecture 38 |
Tor part 1.
|
10:58 | |
| Lecture 39 |
Tor part 2.
|
15:05 | |
| Section 10: ProxyChains for using proxy servers, hiding your ip, and obtaining access. | |||
| Lecture 40 |
Proxychains part 1.
|
12:01 | |
| Lecture 41 |
Proxychains part 2.
|
14:15 | |
| Lecture 42 |
Proxychains part 3.
|
12:57 | |
| Section 11: What is a Virtual Private Network (VPN) and how you can stay anonymous with VPN? | |||
| Lecture 43 |
VPN part 1.
|
13:29 | |
| Lecture 44 |
VPN part 2.
|
14:54 | |
| Section 12: What is a macchanger? How can you use it to change your mac address? | |||
| Lecture 45 |
Macchanger part 1 (updated)
|
17:28 | |
| Lecture 46 |
Macchanger part 2 (updated)
|
19:02 | |
| Section 13: Footprinting with Nmap and external resources. | |||
| Lecture 47 |
Nmap part 1.
|
17:34 | |
| Lecture 48 |
Nmap part 2.
|
19:22 | |
| Lecture 49 |
External resources using public listings of known vulnerabilities.
|
10:11 | |
| Section 14: Attacking wireless networks. Overview of the tools. | |||
| Lecture 50 |
Intro to wifi hacker cracking WPA⁄WPA2.
|
15:14 | |
| Lecture 51 |
Aircrack and reaver installation.
|
12:44 | |
| Lecture 52 |
Installing aircrack-ng on Windows + crunch on Linux.
|
11:34 | |
| Lecture 53 |
For Windows Users. How To Set Up USB wireless Adapter with Virtualbox Part 1.
|
07:42 | |
| Lecture 54 |
For Windows Users. How To Set Up USB wireless Adapter with VirtualBox part 2.
|
07:11 | |
| Section 15: Breaking WPA/WPA2 encryption. Wifi hacking and wifi hacker training. | |||
| Lecture 55 |
Aircrack-ng _ crunch usage example_1
|
11:04 | |
| Lecture 56 |
Aircrack-ng _ crunch usage example_2
|
10:26 | |
| Lecture 57 |
Aircrack-ng _ crunch usage example_3
|
20:39 | |
| Lecture 58 |
Cracking WPS pins with reaver part 1.
|
15:24 | |
| Lecture 59 |
Cracking WPS pins with reaver part 2.
|
10:41 | |
| Lecture 60 |
Cracking WPS pins with reaver part 3.
|
16:25 | |
| Section 16: Signal jamming and denial of service. | |||
| Lecture 61 |
Performing denial of service on wireless networks part 1.
|
13:14 | |
| Lecture 62 |
Performing denial of service on wireless networks part 2.
|
17:55 | |
| Section 17: SSL strips. | |||
| Lecture 63 |
SSL strip part 1.
|
08:49 | |
| Lecture 64 |
SSL strip part 2.
|
10:37 | |
| Lecture 65 |
SSL strip part 3.
|
18:13 | |
| Section 18: Let’s have a bit of fun! | |||
| Lecture 66 |
Funny things part 1.
|
07:03 | |
| Lecture 67 |
Funny things part 2.
|
12:12 | |
| Lecture 68 |
Funny things part 3.
|
18:21 | |
| Section 19: Evil twin method! Clone wireless access points to steal data. | |||
| Lecture 69 |
Evil twin part 1.
|
10:34 | |
| Lecture 70 |
Evil twin part 2
|
07:28 | |
| Lecture 71 |
Evil twin part 3.
|
11:19 | |
| Section 20: Attacking routers to give you free reign over the entire network! | |||
| Lecture 72 |
Using known vulnerabilities part 1.
|
09:40 | |
| Lecture 73 |
Using known vulnerabilities part 2.
|
09:21 | |
| Lecture 74 |
Using known vulnerabilities part 3.
|
18:54 | |
| Section 21: DNS setting hacking to redirect users with post authentication exploitation. | |||
| Lecture 75 |
Post authentication exploitation ( DNS ) part 1.
|
09:38 | |
| Lecture 76 |
Post authentication exploitation ( DNS ) part 2.
|
12:22 | |
| Lecture 77 |
Post authentication exploitation ( DNS ) part 3.
|
13:41 | |
| Section 22: Website attacks with SQL injections. | |||
| Lecture 78 |
sql-injection-part-1
|
12:32 | |
| Lecture 79 |
sql-injection-part-2
|
14:46 | |
| Lecture 80 |
sql-injection-part-3
|
13:22 | |
| Lecture 81 |
sql-injection-part-4
|
11:24 | |
| Lecture 82 |
sql-injection-part-5
|
16:55 | |
| Section 23: Brute-forcing methods for cracking passwords. | |||
| Lecture 83 |
cracking-hashes
|
12:03 | |
| Lecture 84 |
cracking-linux-password-with-john-the-ripper-part-1
|
12:44 | |
| Lecture 85 |
cracking-linux-password-with-john-the-ripper-part-2
|
08:50 | |
| Lecture 86 |
cracking-windows-password-with-john-the-ripper
|
19:25 | |
| Lecture 87 |
hydra-usage-part-1
|
17:13 | |
| Lecture 88 |
hydra-usage-part-2
|
18:21 | |
| Section 24: Denial of Service (DoS) attacks demonstrated and explained. | |||
| Lecture 89 |
DoS attack demonstration part 1. Introduction to Denial of Service attacks.
|
18:37 | |
| Lecture 90 |
DoS attack demonstration part 2. Combine slowloris.pl with nmap.
|
08:19 | |
| Lecture 91 |
DoS attack demonstration part 3 featuring ha.ckers.org.
|
09:45 | |
| Section 25: Reverse shells. Gain remote control of any device! | |||
| Lecture 92 |
Intro to Metasploit and reverse shells. What are reverse shells and why use them
|
18:28 | |
| Lecture 93 |
Metasploit ( reverse shell ) part 2 starting from a two terminal setup.
|
18:24 | |
| Lecture 94 |
Making reverse shells persistent on another system and escalating privileges.
|
16:35 | |
| Lecture 95 |
Creating a persistent reverse shell with Metasploit.
|
10:56 | |
| Lecture 96 |
Using NetCat to make any kind of connection you might need.
|
20:00 | |
| Lecture 97 |
How to upload a reverse shell onto a web server.
|
16:33 | |
| Section 26: Make your own Keylogger in C++ | |||
| Lecture 98 |
General stuff
|
14:15 | |
| Lecture 99 |
Setting up the Environment part 1
|
19:58 | |
| Lecture 100 |
Setting up the Environment part 2
|
19:28 | |
| Lecture 101 |
Programming basics part 1
|
20:08 | |
| Lecture 102 |
Programming basics part 2
|
19:48 | |
| Lecture 103 |
Programming basics part 3
|
14:01 | |
| Lecture 104 |
Programming basics part 4
|
18:38 | |
| Lecture 105 |
Programming basics part 5
|
18:26 | |
| Lecture 106 |
Basic Keylogger part 1
|
20:14 | |
| Lecture 107 |
Basic Keylogger part 2
|
14:37 | |
| Lecture 108 |
Upper and lowercase letters
|
13:58 | |
| Lecture 109 |
Encompassing other characters part 1
|
09:46 | |
| Lecture 110 |
Encompassing other characters part 2
|
10:20 | |
| Lecture 111 |
Encompassing other characters part 3
|
16:07 | |
| Lecture 112 |
Hide keylogger console window
|
10:14 | |
| Section 27: Bonus lectures. | |||
| Lecture 113 |
Bonus lecture with $9 coupons to all the rest of our courses!
|
2 pages | |
Lectures: 113 , Video: 25 Hours , Skill Level: All Levels, Languages: English
AllInOneProxy.com – Use our free proxy to surf anonymously online, unblock any website, secure your internet connection, hide your internet history, and protect your identity – http://allinoneproxy.com/








Thank you very much!!! Really appreciated…
Thanks 😀
file 04 inavailable plz !!!! help :p thx for the work
UsersCloud server 9 is offline please wait for problem fix or Please download from BoxPuff.com screenshot- http://prntscr.com/bwgpsl
File re-upload please check now .
Can you Please provide a Torrent file for the tutorials…
Sorry 🙁
[…] systems. Anyone who’s interested in hacking or security systems can benefit from this welcoming hacking community and in-depth […]